Defense against Kernel Queue Injection Malware
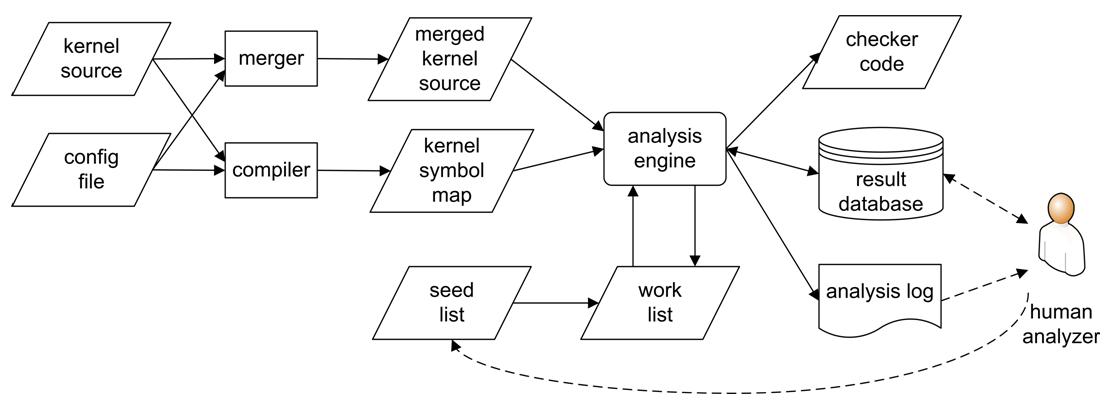
Kernel queue injection (KQI) attacks achieve stealthy malicious function execution by embedding malicious hooks in dynamic kernel schedulable queues (K-Queues) [2]. Because they keep kernel code and persistent hooks intact, they can evade detection of state-of-the-art kernel integrity monitors. Moreover, they have been used by advanced malware such as the Rustock spam bot to achieve malicious goals. To defend against such novel attacks, we propose the Precise Lookahead Checking of function Pointers (PLCP) approach that checks the legitimacy of pending K-Queue callback requests by proactively checking function pointers that may be invoked by the callback function. To facilitate the derivation of specifications for any K-Queue, we build a unified static analysis framework and a toolset that can derive from kernel source code properties of legitimate K-Queue requests and turn them into source code for the runtime checker [1]. A comprehensive defense has been developed for four kernel queues in the Linux kernel [1][3], and a comprehensive defense for the Windows Research Kernel (WRK) is also developed, which protects 20 kernel queues and can support closed source device drivers through dynamic analysis of binary code [4].
Papers:
Jinpeng Wei, Calton Pu. "Towards a General Defense against Kernel Queue Hooking Attacks". Computers & Security, Elsevier Ltd., Volume 31, Issue 2, pp. 176-191, March 2012. doi:10.1016/j.cose.2011.12.007. Download the unofficial version (375 KB).
Jinpeng Wei, Calton Pu, and Keke Chen. "Flying under the Radar: Maintaining Control of Kernel without Changing Kernel Code or Persistent Data Structures". The 7th Annual Cyber Security and Information Intelligence Research Workshop (CSIIRW), October 12 - 14, 2011. Download (54 KB), Slides (123 KB).
Jinpeng Wei, Bryan D. Payne, Jonathon Giffin, Calton Pu. "Soft-Timer Driven Transient Kernel Control Flow Attacks and Defense". In Proceedings of the 2008 Annual Computer Security Applications Conference (ACSAC 2008). Anaheim, CA. December 8-12, 2008. Download (395 KB). Best paper award.
Jinpeng Wei, Feng Zhu, and Calton Pu. "KQguard: Binary-Centric Defense against Kernel Queue Injection Attacks". Proceedings of the 18th European Symposium on Research in Computer Security (ESORICS 2013), Springer-Verlag, Heidelberg, Germany, LNCS 8134, pp. 755-774, 2013. Acceptance rate: 43/242 = 17.8%. Download (396 KB), Slides (522 KB).
Malware analysis reports: LdPinch (62 KB), Matcash (58 KB), Virus DOS Honey 666 (65KB).